The content in this post may be outdated. For the most recent post concerning private Git repositories, please visit the Private Git Repositories series.
Do You Use a Private Git Repo?
Are you looking to deploy your private Git repository to OpenShift Online, and not sure where to start? Don't worry, there's an easy solution for that! In this blog, I'll show how to use your private Git repository with the web console of OpenShift Online.
The key thing is making sure that OpenShift will have the credentials to authenticate itself to the Git repository, so that it can obtain your source code.
The way to do this is to generate and upload a private key to OpenShift, and then to authorize it with your Git hosting provider.
Step 1: Create the Key
First, generate your SSH key if you don't have one. To do this, I recommend following these directions from GitHub.
Key Generation using PuTTY on Windows
Alternatively, if you're using Windows, you can work with PuTTY to generate your SSH keys.
If you’re not familiar, PuTTY is a free and open-source telnet and SSH client, and a standard in the industry. It’s also quite easy to work with for creating and managing your keys.
After installing PuTTY, open up PuTTYgen.
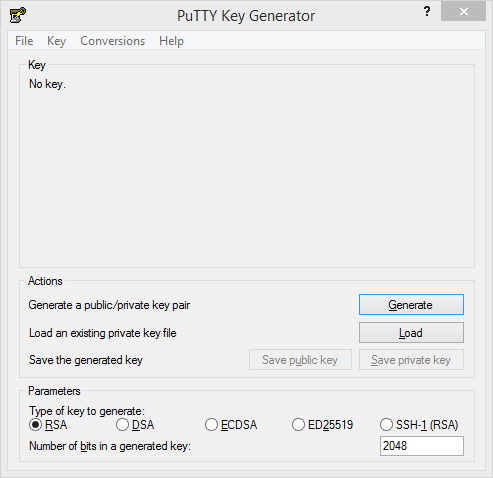
The default settings for PuTTYgen are very secure and should be fine for the purposes of your Git repo. However, there are plenty of resources available if you want to dive deeper into learning about the different authentication methods.
Next, click Generate. Under the Key heading at the top of the window, it’ll ask you to move your mouse over the area to generate some randomness. This will be used to create your key, which will appear momentarily. The key in this field will be your public key. Below that, there will be fields for entering Key passphrase and Confirm passphrase. For OpenShift Online, make sure not to protect your private key with a passphrase and keep those fields blank.
Finally, click Save private key. A text file will be generated that is .ppk format (which can be loaded into PuTTY if needed). Open it up in a text editor (such as Atom), and you’ll see that it has some meta information as well as both your public and private keys. Each key will be below a line that says if it’s public or private, and how many lines, such as Public-Lines: 6, and the private key will end above a line saying Private-MAC. Go ahead and copy your private key for the next step, and have your public key ready to add to the Git repo later.
Step 2: Add the Private Key to an OpenShift Project
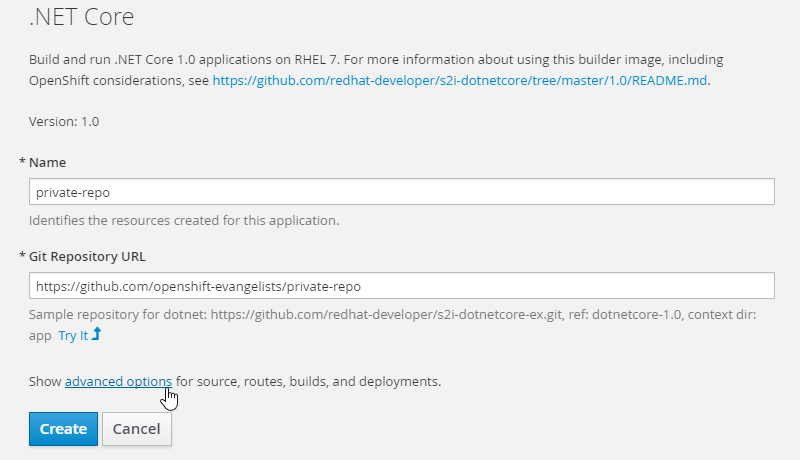
Next, navigate to the OpenShift Online web console and create your project as normal. However, when you go to Add to Project and after you select your language, click on the advanced options link that's above the Create button.
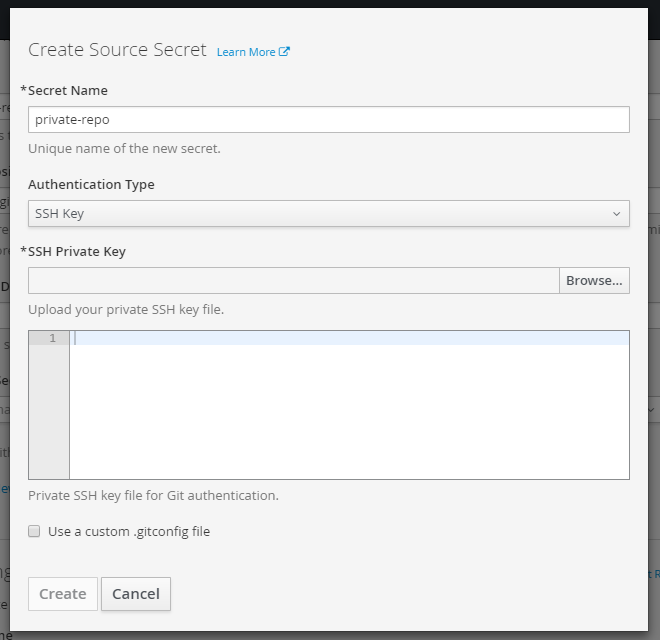
Once there, click on the Create New Secret link. A modal will open where you will need to give your secret a name. Choose "SSH Key" as your authentication type, then paste in your private SSH key file. Click Create and you're done here.
The Source Secret field just above the link should auto-populate with the name of your new secret. Finish up adding to your project and click the Create button at the bottom of the page.
Step 3: Add the Public Key to a Git Repo (or GitHub Profile)
Meanwhile, over on your Git repo, you need to add your public SSH key. You have two alternatives here: You can either authorize the security key in the individual repository (the safer option) or, if you’re using GitHub, you can instead authorize it for all of your repositories (the less secure option). In the first alternative, if your private key were to leak, only a single repository would be affected. This is the recommended method that we’ll explore first.
The More Secure Method
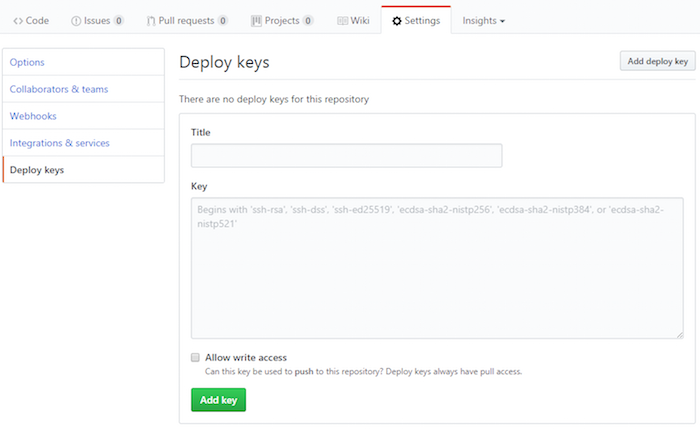
If you’re using GitHub, you can navigate to your private repo, and then select the Settings tab at the top. On the bottom of the left menu, click Deploy keys, and then Add deploy key in the upper right of the page. Add a title for your public key, and then drop it into the Key field. There is also a check box where you can choose whether you want to Allow write access, which means that your public key could be used to push to this repository.
The Less Secure Method
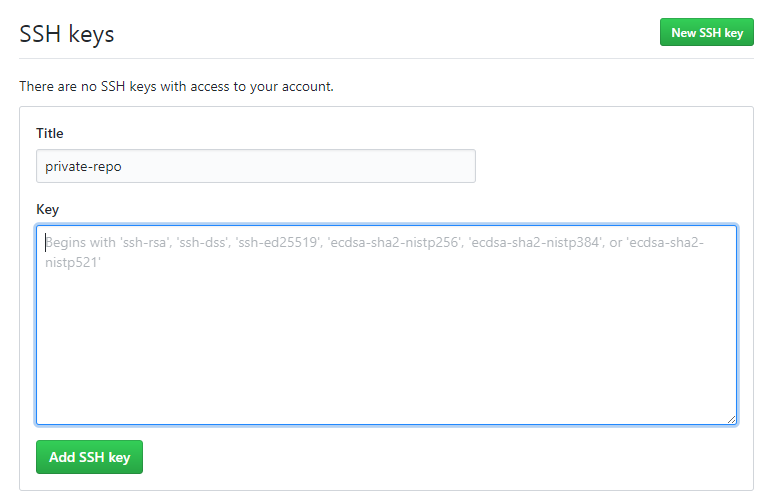
Now, if you want to authorize your security key for all of your Github account (again, I must caution that this could be a security issue should it leak) take these steps: Go to your user profile and in the menu on the left, click SSH and GPG Keys, then the New SSH Key button on the next page. Insert your public SSH key here, and click Add SSH key when finished.
You Did It!
That should do it! Just remember this important distinction: Put your public SSH key in your Git repo or account, and your private SSH key on OpenShift.
If you're interested in adding secrets using the command line, then check out this documentation from OpenShift.
What other topics would be helpful to you in using OpenShift? Leave a comment letting us know, and keep an eye on this blog for more tips!
About the author
More like this
Browse by channel
Automation
The latest on IT automation that spans tech, teams, and environments
Artificial intelligence
Explore the platforms and partners building a faster path for AI
Open hybrid cloud
Explore how we build a more flexible future with hybrid cloud
Security
Explore how we reduce risks across environments and technologies
Edge computing
Updates on the solutions that simplify infrastructure at the edge
Infrastructure
Stay up to date on the world’s leading enterprise Linux platform
Applications
The latest on our solutions to the toughest application challenges
Original shows
Entertaining stories from the makers and leaders in enterprise tech
Products
- Red Hat Enterprise Linux
- Red Hat OpenShift
- Red Hat Ansible Automation Platform
- Cloud services
- See all products
Tools
- Training and certification
- My account
- Developer resources
- Customer support
- Red Hat value calculator
- Red Hat Ecosystem Catalog
- Find a partner
Try, buy, & sell
Communicate
About Red Hat
We’re the world’s leading provider of enterprise open source solutions—including Linux, cloud, container, and Kubernetes. We deliver hardened solutions that make it easier for enterprises to work across platforms and environments, from the core datacenter to the network edge.
Select a language
Red Hat legal and privacy links
- About Red Hat
- Jobs
- Events
- Locations
- Contact Red Hat
- Red Hat Blog
- Diversity, equity, and inclusion
- Cool Stuff Store
- Red Hat Summit